Goldilock
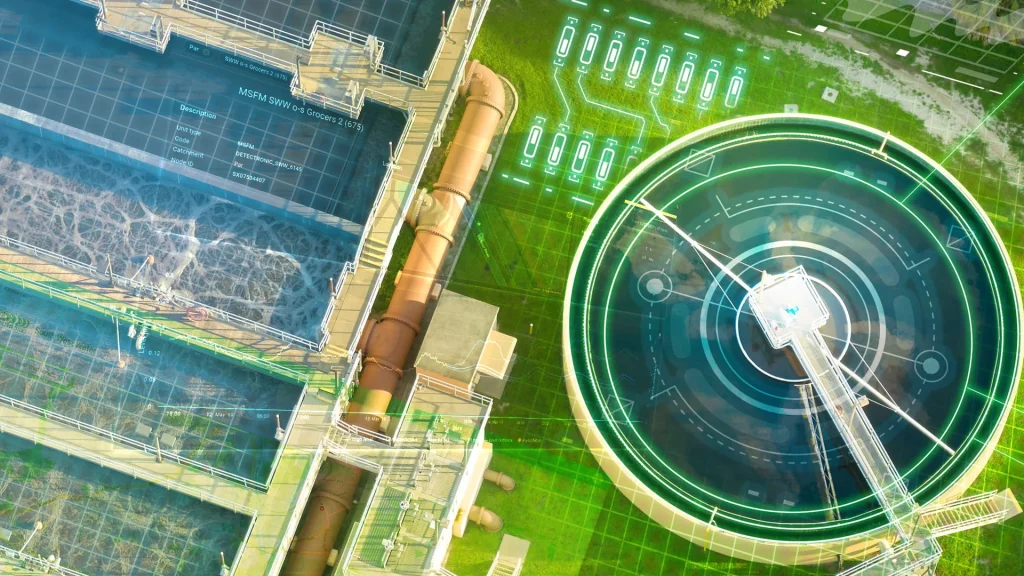
Securing critical networks with physical LAN segmentation technology.
Goldilock FireBreak acts as a layer-1 network circuit breaker, physically isolating Critical Infrastructures and OT networks.
In the event that a security threat or breach of a network is detected by existing security tools, Goldilock gives an instant capability to isolate any high value asset or critical infrastructure from data access.
Goldilock uses an out-of-band, non-IP signalling technology that is not accessible from the Internet, keeping the management and command pathway out of sight and reach of external threat actors
Goldilock FireBreak is an essential failsafe technology to help organisations deliver improved protections or recovery from cyber-attacks. Physical isolation of mission critical networks, enables the organisation the ability to regain full and physical control of their infrastructure and attack surface.
How does FireBreak work?
Goldilock FireBreak uses patented technology that is unmatched.
Utilising Reed switches, they are able to physically disconnect the data layer in seconds on a per port basis, through its most simplest form of prising metal contacts apart when a signal is triggered.
Golidlock is not controlled through software, but instead triggered remotely through the short messaging service (SMS), paired with 2FA/OTP authentication.
Technical Specifications
They are offered in 4 port small form factor or 12 port 1u rack mount versions, each appliance includes RJ45 Ethernet connectivity with uncontended 10 Gb data throughout.

TAC Product Evaluation Report

Technology Advancement Center (TAC), formerly MISI, completed a technical evaluation of the Goldilock appliance.
(TAC) are a nonprofit cybersecurity organisation, supporting and fuelling the people and technology needed to solve critical cybersecurity challenges.
General Use Cases
Ransomware Response and Recovery
- Immediately and remotely disconnect networks under attack to stop spread.
- Isolate back-ups from being compromised to aid faster recovery.
Integral Network/Data Segregation
- Shield high risk networks or data that contains Intellectual Property or personal identifiable information, industrial control systems, create secure digital vaults, or protect cryptographic keys and wallets.
Control Untrusted Third-Party Networks
- Avoid ‘always-on’ access to critical networks and mitigate risks of indirect cyber-attacks.
- Permit time limit network access to critical assets for authorised contractors/3rd parties, after which, assets can be automatically disconnected.
DevOps Segregation
- Create a secure procedure between development, testing and production.
Schedule a Demo
Request a demo today in the form below. We can show you how simple ring-fencing key infrastructure or taking key network components on and offline are.
Alternatively you can email us on sales@cyberdistribution.co.uk